OpenClaw tutorials, troubleshooting, and security guides
Mar 28, 2026·7 min read

OpenClaw TikTok Marketing: How the Larry Skill Works
OpenClaw TikTok marketing via the Larry skill: 6-slide formula, image gen, Postiz feedback loop, and hook iteration that drove 500K views in 5 days.
Mar 26, 2026·5 min read

How TwainGPT Humanizer Actually Works: Unicode Analysis
How TwainGPT humanizer works, whether it uses unicode substitution, and what the evidence actually shows about bypassing AI detectors.
Mar 25, 2026·7 min read
Recent Posts
View all →
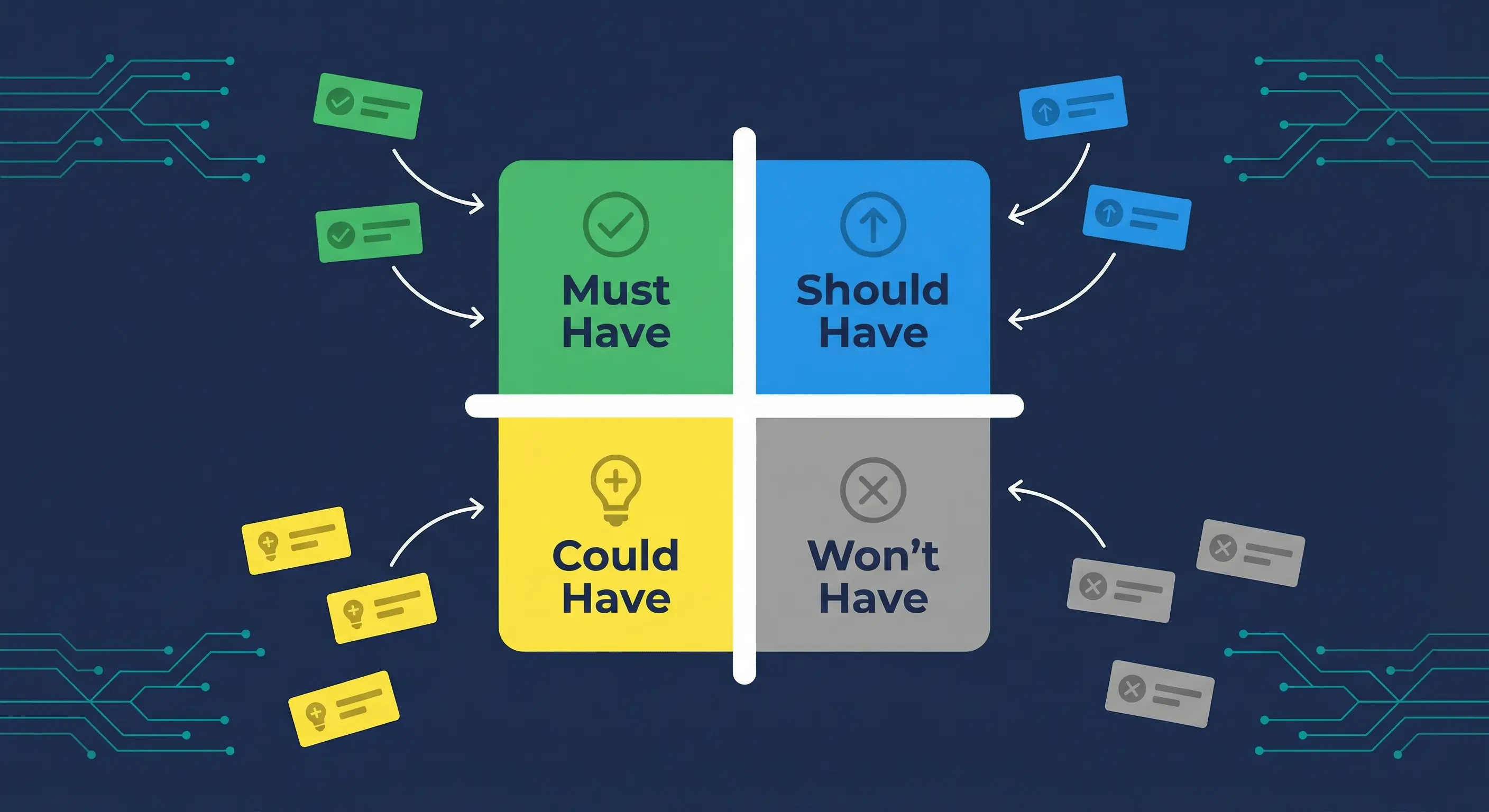
MoSCoW Prioritization When Everything Feels Must-Have
MoSCoW breaks when every feature lands in Must Have. Here are the session steps, hard conversations, and scope cuts that worked.
Mar 24, 2026·7 min read

Solo Developer App Release Checklist: Step-by-Step
Solo developer release checklist covering testing, store submission for Google Play and Microsoft Store, launch prep, and post-launch monitoring.
Mar 24, 2026·6 min read

Why Free Apps Actually Cost You More Than Paid Ones
Free apps cost you attention, data, and dark-pattern upgrades. Here is the real math on what ad-supported and freemium apps actually extract from users.
Mar 24, 2026·6 min read

App Monetization Dark Patterns That Punish Free Users
App monetization dark patterns manipulate free users into paying with countdown timers, artificial limits, and buried cancellation flows. Here are the real offenders.
Mar 23, 2026·6 min read

Migrate from Claude Code to OpenClaw: Step-by-Step
Migrate from Claude Code to OpenClaw in 4 steps. Map CLAUDE.md to AGENTS.md, connect channels, configure cron, and run persistent subagents.
Mar 23, 2026·7 min read
